Introduction
In January 2025, the Digital Operational Resilience Act came into full effect. It sets a clear standard for how financial entities manage ICT risk. Under DORA requirements, firms must demonstrate that they can withstand, respond to, and recover from ICT disruptions. This includes the failure or discontinuation of critical third-party software providers.
For many institutions, this risk sits in vendor-dependent systems. Core banking platforms, trading systems, and compliance tools often rely on external providers. If a vendor fails, operations can stop.
DORA software escrow provides a direct, contract-level control to support software continuity for DORA. It gives financial entities a structured way to access source code and critical materials when a vendor cannot deliver. This guide explains how escrow supports DORA compliance and software escrow requirements in practice.
What Is DORA and Who Does It Apply To?
Scope of the Regulation
The Digital Operational Resilience Act is an EU regulation that standardizes ICT risk management across financial services. It sets clear requirements for financial entities operating in or serving the EU.
It applies to:
- Banks and credit institutions
- Insurance companies
- Investment firms
- Payment institutions
- Crypto-asset service providers
- Fintech companies operating in or serving the EU
These DORA compliance requirements also apply to third-party providers. If a non-EU vendor delivers critical ICT services to an EU financial entity, that relationship falls within scope. This makes vendor contracts and enforceable controls central to DORA compliance and software escrow strategies.
ICT Third-Party Risk as a Core Pillar
DORA places strong focus on DORA third party risk management. Financial entities must implement structured and enforceable controls.
Key requirements include:
- Managing concentration risk
- Defining exit strategies for critical vendors
- Ensuring continuity of critical ICT systems
These controls must work under real failure conditions.
Many institutions rely on a single SaaS provider for critical functions such as trading or anti-money laundering monitoring. This creates a single point of failure. Firms must identify and mitigate this risk.
Why Does This Matter for Software-Dependent Systems?
Most financial infrastructure relies on third-party software. Vendor stability directly affects system availability.
Common failure scenarios include:
- Vendor insolvency
- Extended application downtime
- Product discontinuation
- Licensing disputes or restricted access
Without safeguards, vendor failure leads to system failure.
DORA requires firms to plan for these outcomes as part of a structured DORA compliance checklist. This makes software continuity for DORA a practical requirement.
DORA software escrow supports this by providing controlled access to source code and critical materials. It allows financial entities to maintain or restore systems when a vendor cannot deliver.
Where Software Escrow Fits in DORA Compliance?
Mapping Escrow to DORA Requirements
The Digital Operational Resilience Act includes provisions that align with software escrow.
Key articles include:
- Article 28: ICT third-party contractual arrangements and exit strategies
- Article 30: Key contractual provisions for business continuity
These require financial entities to define how they will maintain operations if a critical ICT provider fails.
This is where DORA compliance and software escrow connect. Escrow enforces these requirements at the contract level by securing access to source code, documentation, and deployment materials under defined release conditions.
How Escrow Reduces Vendor Risk?
Software escrow reduces dependency risk by ensuring access when a vendor cannot deliver.
If a vendor:
- Becomes insolvent
- Discontinues a product
- Breaches contractual obligations
The financial entity can access the deposited materials.
This enables:
- Internal system maintenance
- Migration to an alternative solution
- Rebuilding the application environment
For example, if a payments platform vendor shuts down, escrow allows continued operation during transition.
This is a direct use of DORA software escrow in a failure scenario. It also supports software continuity for DORA by keeping systems operational during disruption.
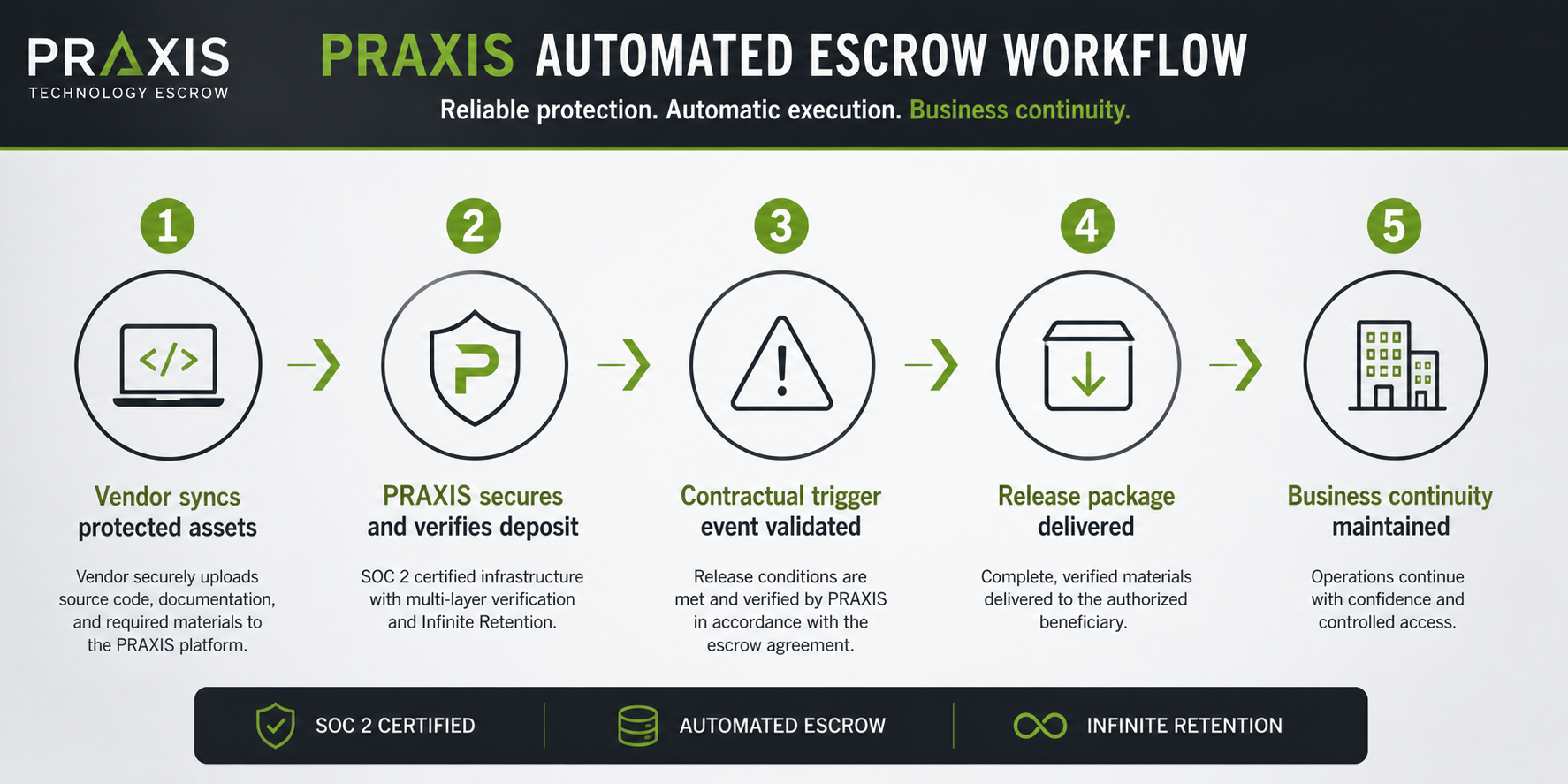
In advanced implementations, active escrow DORA compliance includes automated deposits and structured release conditions aligned with development workflows.
What Escrow Does NOT Replace?
Escrow is one control within a broader framework. It does not replace core risk management processes.
Financial entities must still implement:
- Vendor risk assessments
- Ongoing monitoring
- Incident response planning
Escrow ensures access when needed. It does not prevent vendor failure or detect early risk.
Under DORA compliance requirements, escrow acts as a safeguard. It activates when other controls can no longer maintain continuity.
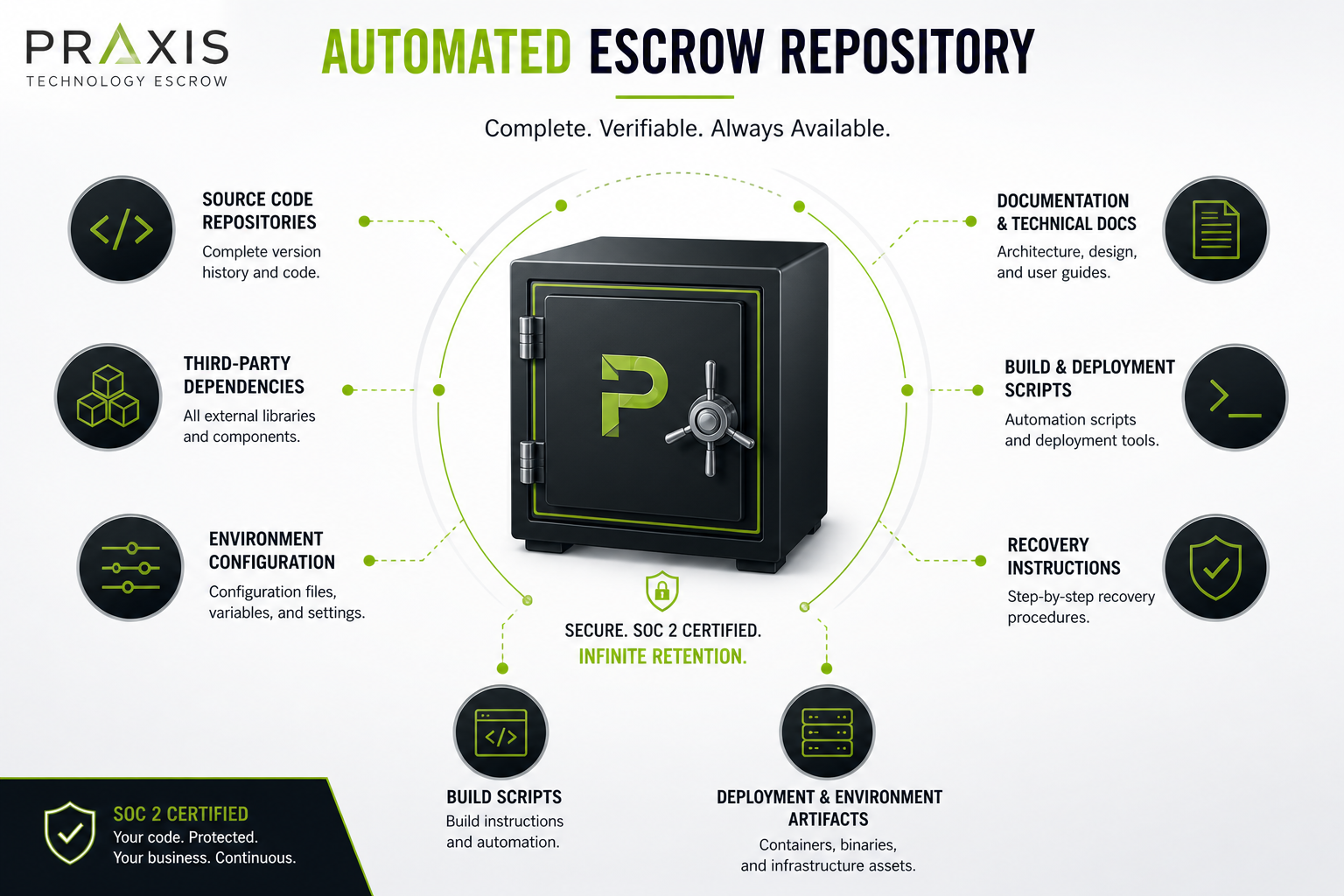
What DORA-Ready Software Escrow Should Include
Core Deposit Components
A DORA-ready escrow deposit must be complete and usable. It must support recovery, not storage.
This includes:
- Full, buildable source code
- Build instructions and environment configurations
- Data schemas and database structures
- Third-party dependencies and licensing details
- An updated data backup
The deposit must be buildable and deployable to support software continuity for DORA.
Operational Requirements (Continuity in Practice)
Escrow must reflect the current state of the software. Outdated deposits cannot support recovery.
This requires:
- Regular updates aligned with production releases
- Version control with full history
- Defined processes to maintain accuracy
Stale deposits create risk because they do not match live systems. Deposits must stay current through structured updates.
Verification and Active Escrow
Verification ensures that escrow materials are usable.
It includes:
- Technical validation that the code can be built
- Environment testing for dependencies and configurations
- Ongoing checks to confirm accuracy
This is the difference between passive storage and active escrow DORA compliance.
Without verification, there is no assurance that the deposit will function during a failure. Verification also supports audit readiness by providing evidence that recovery is possible.
Release Triggers and Legal Clarity
Escrow agreements must define clear and enforceable release conditions.
Common triggers include:
- Vendor insolvency
- Material breach of contract
- Product discontinuation
The agreement should also define:

- Notification procedures
- Release timelines
- Roles and responsibilities of each party
Under DORA compliance requirements, release conditions must align with contractual obligations and be enforceable.
DORA Compliance Checklist (Escrow Readiness)
A structured review helps confirm whether escrow supports compliance:
- Is the source code complete and buildable?
- Are deposits updated with each release?
- Has verification been performed regularly?
- Are release triggers clearly defined and enforceable?
This aligns with a practical DORA compliance checklist and supports audit preparation.
How to Include Escrow in DORA-Compliant Vendor Contracts?
Contract Structure and Requirements
Escrow must be defined in the vendor contract. It should not sit outside the agreement or be added later.
The contract should include:
- The named escrow agent
- Defined deposit obligations, scope of materials and release conditions
- A clear reference to the escrow agreement within the main contract
For critical systems, this is a standard control. It embeds continuity at the contractual level and supports DORA compliance and software escrow.
This approach aligns with core DORA requirements for managing third-party ICT risk.
Control and Enforcement Mechanisms
Contracts must ensure that the financial entity retains control over escrow processes.
Key provisions include:
- The right to initiate verification
- The ability to trigger release under defined conditions
- Clear notification procedures
Control should not sit only with the vendor. If the vendor controls verification or release, the safeguard fails.
Under DORA compliance requirements, controls must be enforceable. The financial entity must be able to act without vendor approval during a failure event.
This ensures escrow supports software continuity for DORA in real conditions.
Procurement Best Practices
Escrow should be introduced during the evaluation process and completed by procurement, not after contract execution.
Best practices include:
- Including detailed escrow and verification requirements in RFPs
- Aligning legal, procurement, and technical teams early
- Treating escrow as a baseline requirement for critical vendors
- Executing the escrow agreement along with the subscription or license agreement
This strengthens DORA third party risk management by addressing continuity risk during vendor selection.
When escrow is built into procurement, it becomes part of standard vendor governance, not a late-stage negotiation.
DORA Audit Readiness and Escrow Documentation
What Regulators Expect to See
The Digital Operational Resilience Act requires financial entities to demonstrate how they manage ICT risk. This includes clear documentation of third-party software dependencies and continuity controls.
For escrow, documentation should show:
- Which critical systems are covered by escrow agreements
- Why those systems are classified as critical
- How escrow supports continuity and risk mitigation
- The role of the escrow agent in holding and releasing materials
This documentation should align with the firm’s system inventory and risk classification framework. It should show how escrow supports DORA compliance and software escrow in practice.
Evidence of Ongoing Compliance
DORA requires continuous oversight. Controls must remain active and current.
Escrow should produce:
- Verification dates, logs, and technical results
- Deposit update history aligned with releases
- Clearly defined and documented release triggers
These records confirm that escrow is maintained over time. They support active escrow DORA compliance by ensuring deposits are usable and current. They also align with DORA compliance requirements.
Escrow as Audit-Proof Documentation
A structured escrow program provides audit-ready documentation.
It demonstrates:
- Continuity planning for critical systems
- Third-party risk mitigation
- Functional controls supported by verifiable records
This aligns with a practical DORA compliance checklist used during internal reviews and regulatory audits.
Escrow becomes a defensible control. It shows that the organization can maintain operations if a vendor fails.
Closing
DORA compliance requires ongoing management of ICT third-party risk. Controls must work under real conditions, not just on paper. DORA software escrow provides a practical way to maintain system availability if a critical vendor fails. It supports continuity at the contract level and aligns with core DORA requirements.
PRAXIS helps financial entities assess where escrow is needed, what deposits should include, and how agreements should be structured to meet audit expectations. Start with a review of your critical ICT vendor portfolio.
Frequently Asked Questions
What is DORA and why does it matter for software escrow?
DORA is an EU regulation that requires financial entities to manage and recover from ICT disruptions, including third-party failures. The Digital Operational Resilience Act, effective January 2025, sets enforceable standards for operational resilience. DORA software escrow ensures access to critical systems if a vendor cannot deliver.
Which DORA provisions does software escrow help address?
Software escrow supports Article 28 and Article 30 of DORA. These cover contractual arrangements, exit strategies, and business continuity. They are part of DORA compliance requirements for managing third-party ICT risk.
What should a DORA-compliant software escrow deposit include?
A compliant deposit must be complete and buildable. It includes source code, documentation, dependencies, and environment configurations. Regular updates and verification support active escrow DORA compliance.
How do financial entities include escrow requirements in vendor contracts for DORA?
They define deposit obligations, release triggers, and verification rights in vendor contracts. This ensures control during failure events. Strong DORA compliance and software escrow structures place control with the financial entity.
Does software escrow alone satisfy DORA ICT third-party risk requirements?
No. Escrow is one control within a broader framework. It supports software continuity for DORA but must be combined with risk assessments, monitoring, and incident response planning.

Chris Smith Author
Chris Smith is the Founder and CEO of PRAXIS Technology Escrow and a recognized leader in software and SaaS escrow with more than 20 years of industry experience. He pioneered the first automated escrow solution in 2016, transforming how escrow supports Agile development, SaaS platforms, and emerging technologies.

