Introduction
Software escrow negotiation often fails due to mismatched expectations between buyers and vendors. Buyers expect full continuity. Vendors expect limited obligations.
This gap creates friction. Agreements stall over unclear deposit scope, vague release triggers, and undefined costs. Phrases like “source code and related materials” sound complete but often exclude what is required to compile and run the system.
This guide provides a practical software escrow agreement negotiation checklist. It explains how to negotiate an escrow agreement by focusing on three points: what is deposited, when it is released, and whether it will work when needed.
Deposit Scope — What’s Actually Going In?
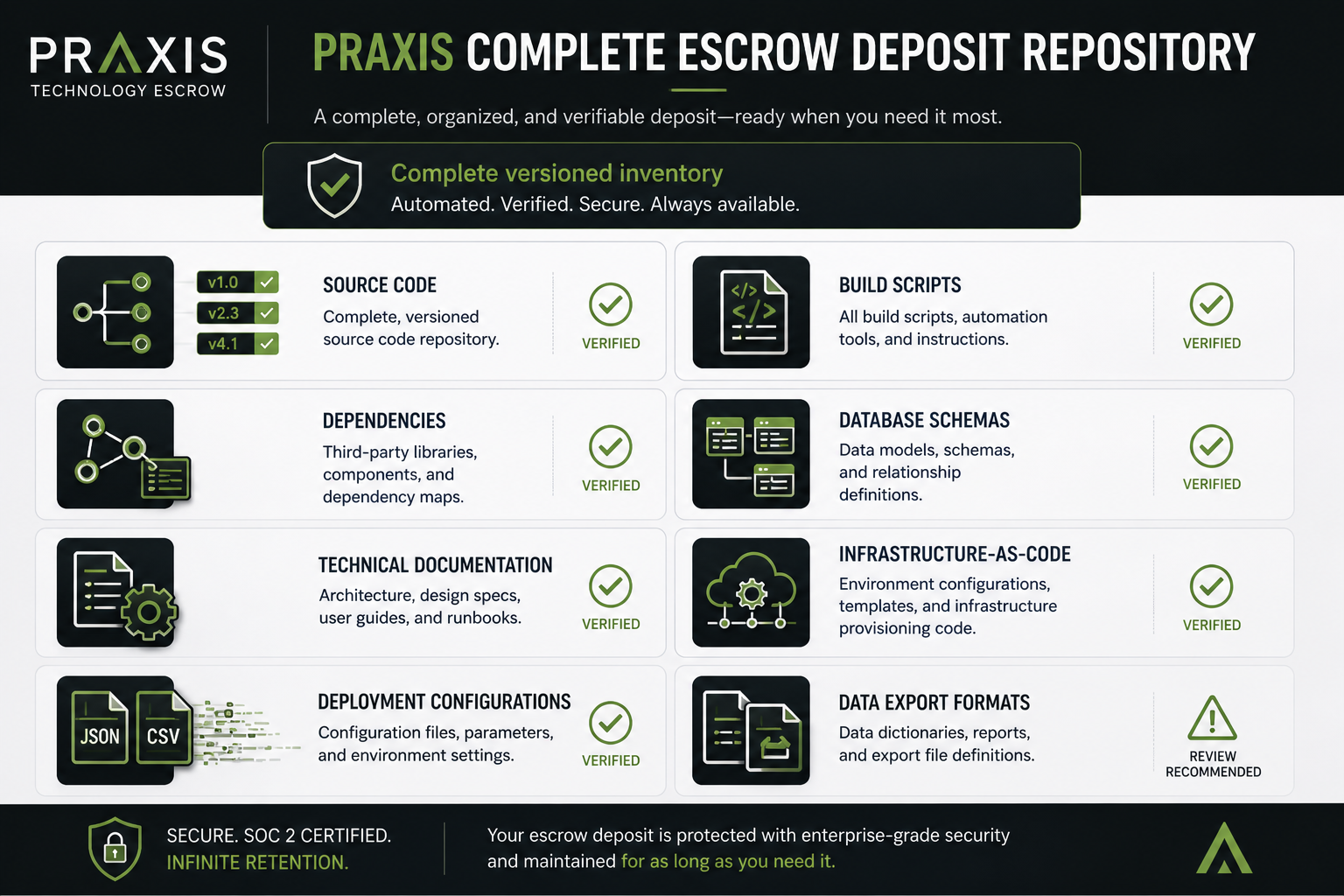
Deposit scope defines what is included in escrow and whether the software can operate independently.
In software escrow negotiation, this is the most common point of contention. Buyers expect continuity, while vendors aim to limit disclosure to what is necessary.
Buyers need a deposit that supports operation and maintenance without vendor support. Vendors need to protect proprietary logic. A clear, defined scope balances both.
A complete escrow deposit should include a versioned inventory:
- Source code with defined modules and branches
- Build scripts and environment configurations
- Third-party dependencies and licensing details
- Database schemas and migration logic
- API documentation and operational runbooks
Each component must be explicitly to the extent possible. However, necessary deposit materials can change as the SaaS application or software evolves. Thus, a general obligation for the Vendor to deposit “everything a reasonably skilled software engineer to build and support the software” can be helpful in broadening the responsibility on the Vendor. This bar is an established industry standard.
For SaaS applications, additional components are required. This is a key consideration in SaaS escrow negotiation:
- Infrastructure as code
- Deployment configurations and environment variables
- Defined data export procedures
These elements ensure the system can be recreated in a new environment.
A common risk is vague language such as “source code and related materials” without a defined inventory. This often excludes critical components like build scripts, dependencies, and configurations, which only becomes apparent when escrow is released.
Release Triggers — When Does the Escrow Activate?
Escrow activates when predefined release conditions are met, such as vendor failure, breach, or discontinuation of support. In software escrow negotiation, buyers prefer broader triggers while vendors prefer narrower ones. The goal is to define triggers that are clear and enforceable.
Standard triggers both sides should accept:
- Vendor insolvency or bankruptcy
- Material breach of the license agreement that remains uncured after notice
- Vendor ceases support or maintenance of the software
- Vendor acquisition with stated intent to discontinue the product
Some triggers require defined thresholds:
- SLA failures with clear uptime or performance thresholds
- Change of control, where acquisition alone does not trigger release
These triggers must be tied to measurable and objective conditions.
Trigger conditions to avoid:
- Triggers that are too narrow to ever activate
- Triggers that are too broad and activate during routine business changes
Balanced trigger design is essential in technology escrow contract negotiation.
Verification — Who Checks That the Deposit Is Usable?

The escrow agent or an independent technical reviewer checks whether the deposit is usable. Verification ensures the escrow deposit can be compiled and deployed when needed. Depositing code alone is not enough. A deposit that cannot be built or run does not provide continuity. This is a common gap in software escrow negotiation, where agreements define deposits but not how they are validated.
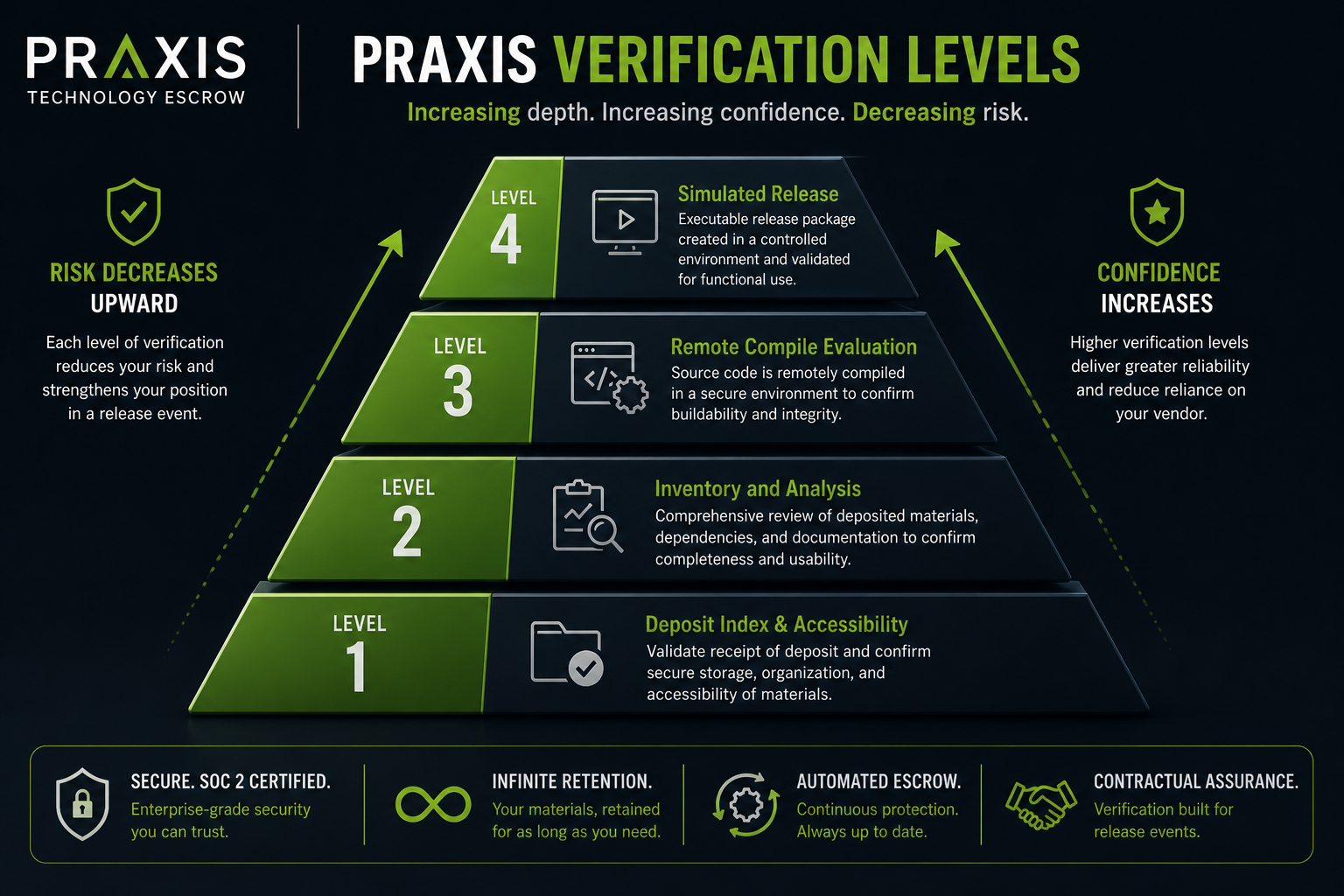
Verification typically involves different levels of review:
- Basic verification: the escrow agent confirms files are received and readable
- Technical verification: an independent review confirms the code is complete and buildable
- Full rebuild verification: the deposit is compiled and tested in a clean environment
For critical systems, technical or rebuild verification is required.
Verification is performed by the escrow provider or an independent reviewer. Costs are usually assigned to the requesting party or shared between both parties. This should be defined clearly when teams negotiate software escrow agreement terms.
Annual technical verification is standard for critical systems. More frequent verification is needed for actively developed software or SaaS environments. This is an important consideration in SaaS escrow negotiation.
Most agreements define deposit scope but not verification. Without scheduled verification, there is no assurance the deposit will function when released. Buyers should require defined methods and frequency as part of a software escrow agreement negotiation checklist.
Fees — Setup, Annual, and Verification Costs
Software escrow fees typically include setup, annual maintenance, and verification costs.
In software escrow negotiation, disputes usually come from how costs are allocated and what each fee covers.
Most agreements include three types of fees:
- Setup fees for agreement drafting and the initial deposit
- Annual fees for ongoing storage and administration
- Verification fees charged per verification event
Each category should be clearly defined and tied to specific services.
Cost allocation varies between buyer and vendor. In some agreements, the vendor pays all fees. In others, the buyer pays verification costs or fees are shared. Allocation should reflect who benefits from each service.
The agreement should also define responsibility for each fee, what services are included, and how fees can change over time. Clear terms reduce disputes in technology escrow contract negotiation.
Common risks include paying annual fees without the ability to request verification, undefined price increases, and additional charges tied to release or validation. These issues reduce the practical value of escrow.
To control costs, agreements often cap annual increases using an index such as CPI and link verification fees to defined outcomes. When evaluating how to negotiate software escrow fees, each cost should support a usable result.
Beneficiary Rights and Notification
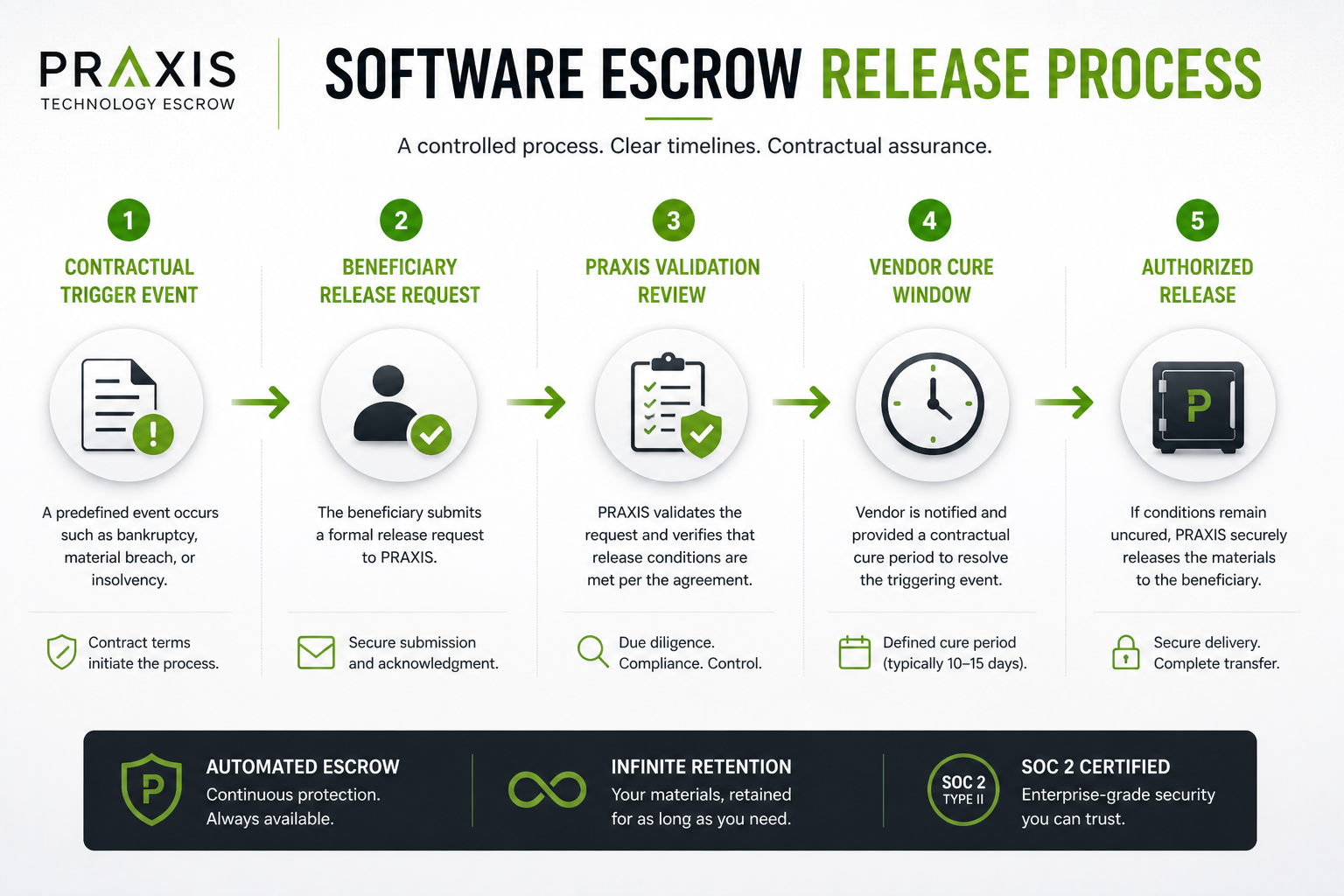
Beneficiary rights define who can initiate a release and how the process moves once a trigger occurs.
In software escrow negotiation, delays often happen when roles and responsibilities are not clearly defined.
The beneficiary is the software licensee, but the agreement must specify the exact legal entity. It should also clarify whether affiliates, subsidiaries, or successors are included. Without this, the wrong entity may be blocked from initiating a release.
The notification process must be defined clearly. This includes who contacts the escrow agent, what documentation is required to prove a trigger event, and how quickly the request must be acknowledged. Without defined steps, the process can stall.
Most agreements allow the vendor to contest a release request. This is standard, but the timeline and process must be controlled. The agreement should define response windows and escalation steps to prevent indefinite delays.
In multi-licensee escrow arrangements, one customer’s release request may affect others. The agreement should define:
- How access is granted across multiple beneficiaries
- Whether rights are segmented or shared
Common risks include undefined beneficiary scope, missing notification procedures, and open-ended dispute timelines. These gaps can prevent execution when escrow is needed most.
SaaS Escrow Negotiation — What Changes in Cloud Environments?
SaaS escrow requires additional terms beyond traditional software escrow. In software escrow negotiation, access to code is not enough. The system must be able to run in a new environment after release.
Data portability must be defined clearly. The buyer needs access to usable data, not just raw exports. This includes format, frequency, and supporting schema documentation. Without this, data cannot be restored or used effectively.
Hosting and infrastructure requirements must also be documented. SaaS applications depend on specific environments. The agreement should define cloud configurations, infrastructure-as-code, and system dependencies required to run the application.
API and integration dependencies must be included. SaaS platforms often rely on external services. These connections need to be documented so the system can function after release.
Transition planning is critical. Release is the starting point, not the end of the process. The agreement should define:
- A transition window, often 30 to 90 days
- Vendor or successor obligations for transition support
- Required documentation to deploy and operate the system
Common risks include vague data access terms, missing infrastructure definitions, and no transition support. These gaps prevent the system from operating after release.
In SaaS escrow negotiation, continuity depends on operability, not just access.
Getting to a Workable Agreement
A well-structured software escrow negotiation ensures both parties understand their obligations and protections. Buyers gain continuity. Vendors define clear and limited responsibilities.
The terms that matter most are deposit scope, release triggers, and verification. Getting these right at the contract stage reduces risk and prevents disputes later.
Praxis works with buyers and vendors to structure escrow agreements that are practical and enforceable. Start with a review of your current terms or define what a new agreement should include.
Frequently Asked Questions
What are the most important terms to negotiate in a software escrow agreement?
Deposit scope, release triggers, verification, and fees are the core terms in any software escrow negotiation. Most disputes come from vague scope such as “source code and related materials” and missing verification. Each term must be clearly defined and testable.
What should a software escrow deposit include?
A complete deposit includes source code with defined branches, build scripts, dependencies, database schemas, and operational documentation. For SaaS, include infrastructure-as-code, deployment configurations, and data export procedures. The deposit must be buildable in a clean environment to be usable.
What are standard software escrow release triggers?
Common triggers include vendor bankruptcy, material breach after a defined cure period, support termination, and acquisition with intent to discontinue. SLA-based triggers should use clear thresholds, such as uptime dropping below 99.5% for 60 consecutive days, to ensure enforceability.
Who pays for software escrow verification?
The requesting party usually pays, though costs may be shared or covered by the vendor.
What matters is that verification rights are included. Paying annual fees without the ability to verify the deposit is a common failure point.
How is SaaS escrow negotiation different from traditional software escrow?
SaaS escrow negotiation focuses on operability, not just access. This includes defined data exports, often monthly in formats such as JSON or CSV, infrastructure requirements, and a transition window of 30 to 90 days. Without these, releasing the code will not restore the system.

Chris Smith Author
Chris Smith is the Founder and CEO of PRAXIS Technology Escrow and a recognized leader in software and SaaS escrow with more than 20 years of industry experience. He pioneered the first automated escrow solution in 2016, transforming how escrow supports Agile development, SaaS platforms, and emerging technologies.

