Introduction
Software supply chain attacks are now operational risks. Incidents such as Log4Shell showed how a single vulnerable dependency can affect thousands of systems. In response, regulators introduced stricter requirements. U.S. Executive Order 14028, CISA guidance, and the EU Cyber Resilience Act have made SBOM adoption part of procurement and compliance workflows.
Most organizations use SBOMs for software bill of materials cyber security. They improve software supply chain transparency by identifying components and vulnerabilities. However, SBOMs do not ensure continuity. They show what is in the software, not how to recover it. This is where SBOM software escrow provides a practical solution.
What Is an SBOM?
A Software Bill of Materials (SBOM) is a machine-readable inventory of all components in a software product. It includes open-source libraries, third-party dependencies, proprietary modules, version information, and licensing details.
SBOMs are a core part of the software bill of materials in cyber security. When a vulnerability such as Log4Shell is disclosed, an SBOM allows teams to identify affected systems quickly. This reduces response time and improves risk visibility.
SBOMs also support software supply chain transparency. They show where components originate and how they are assembled. This improves understanding of software provenance and escrow considerations during vendor evaluation.
Regulatory adoption is increasing:
- U.S. Executive Order 14028 requires SBOMs for federal software suppliers
- CISA promotes SBOM use for supply chain risk management
- The EU Cyber Resilience Act requires SBOMs for products with digital elements
However, an SBOM has a clear limitation. It documents what is in the software, but it does not provide a way to rebuild or operate it if the vendor is no longer available.
What SBOMs Don’t Solve: The Continuity Gap
An SBOM answers one question: what is in the software. It does not answer what happens if the vendor cannot deliver.
If a vendor shuts down, is acquired, or stops supporting a product, the SBOM does not provide usable code, build instructions, or deployment assets. It shows the components, but it does not allow the system to run.
This is where SBOM and business continuity breaks down. SBOMs support risk visibility, not recovery. They help identify dependencies, but they do not enable response to vendor failure.
Consider a critical SaaS provider going offline. The SBOM shows which components were used, but it does not provide the source code or environment needed to recreate the system. Availability becomes the primary risk.
For true SBOM software continuity, organizations need the ability to rebuild and operate the software independently.
What Is Software Escrow and How Does It Complement an SBOM?
Software escrow is a legal and technical arrangement where a verified copy of source code, build assets, and documentation is held by a neutral third party. If predefined conditions are met, such as vendor failure, the licensee can access and use these materials.
The distinction is clear:
- SBOM provides inventory and software supply chain transparency
- Escrow provides recovery and continuity
Together, they form a software bill of materials escrow model that supports both visibility and execution.
An SBOM shows what is in the software. Escrow ensures the software can be rebuilt and used if the vendor is no longer available. One without the other creates a gap.
How SBOM Software Escrow Works in Practice
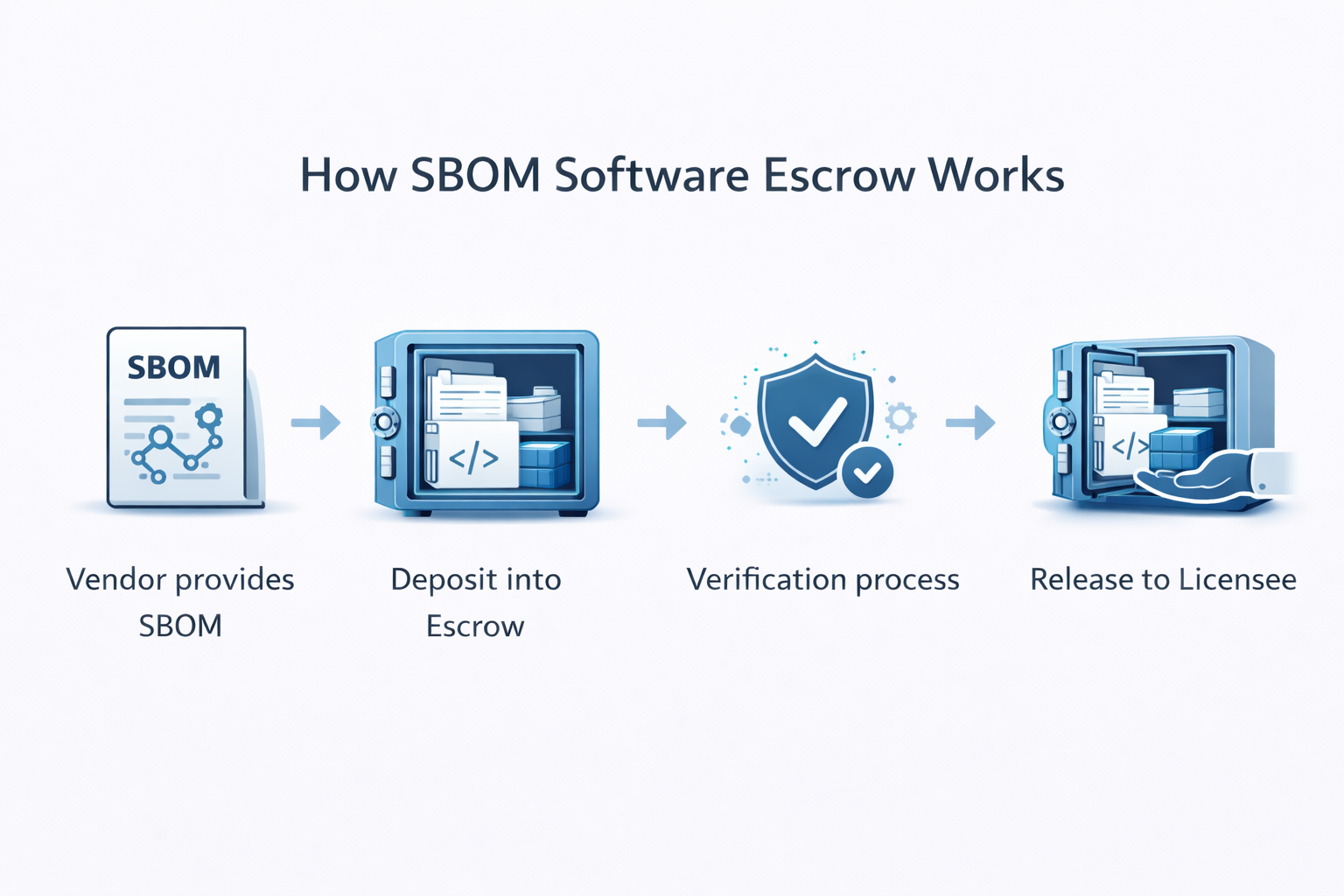
In practice, SBOM software escrow follows a structured process:
- The vendor delivers an SBOM during procurement or compliance
- Source code, dependencies, and build assets are deposited into escrow
- The escrow provider verifies that the software can be rebuilt
- If a release condition is triggered, the licensee receives access to the materials
The SBOM and escrow deposit must align to the same software version. This ensures that documented components match what can be rebuilt and deployed.
What Should Be Escrowed Alongside an SBOM?
An SBOM provides a map of the software. Escrow must include everything required to follow that map and rebuild the system.
Core Deposit Components
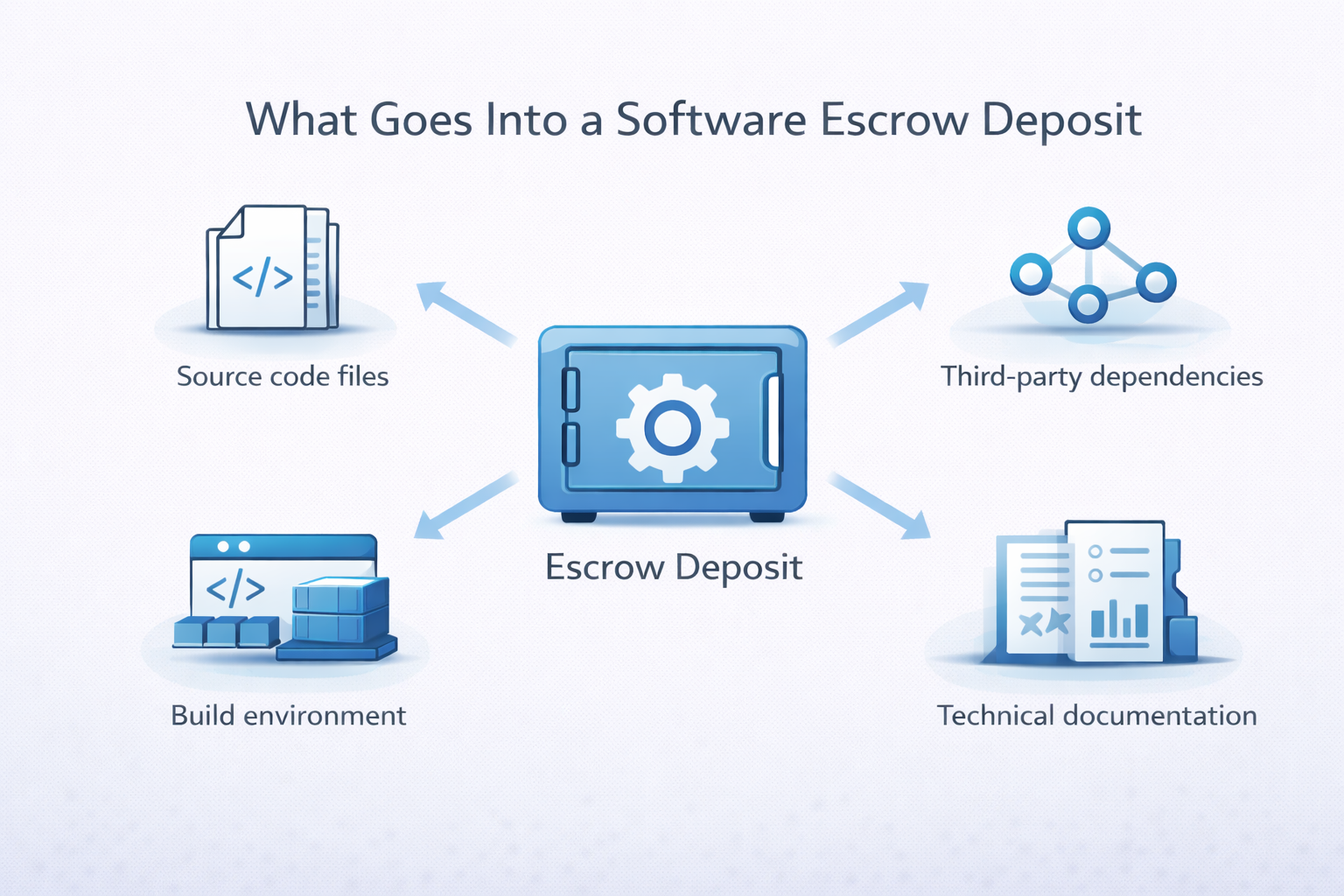
A complete escrow deposit should include:
- Source code: The full, version-controlled codebase
- Third-party dependencies: Exact versions referenced in the SBOM
- Build environment: Compilers, scripts, and container configurations required to compile the software
- Documentation: Architecture, deployment, and configuration details
This ensures SBOM software continuity by enabling actual rebuild, not just documentation.
Why Verification Matters
Escrow is only useful if the deposit works. Verification confirms that the code builds, dependencies resolve, and the system runs as expected.
Without verification, deposits may fail when needed. Dependencies can change, repositories can be removed, and build steps can be incomplete.
This is where software provenance and escrow connect. The SBOM identifies components and their origins. Escrow preserves those versions and verifies they can be used. Together, they create a reliable recovery path.
Who Should Require SBOM Software Escrow in Contracts?

Organizations that rely on critical third-party software should include SBOM software escrow in vendor requirements. This is most relevant where system availability and supply chain risk are high.
This includes:
- Enterprise buyers managing business-critical systems
- Regulated industries such as financial services, healthcare, defense, and critical infrastructure
- Government contractors subject to U.S. Executive Order 14028 or NIST SSDF requirements
These requirements should be defined early in the procurement process.
They typically appear in:
- RFP and procurement documentation
- Vendor risk management frameworks
- Zero-trust and supply chain risk programs
For organizations focused on SBOM and business continuity, escrow should be a standard contract requirement. It should not be added after vendor selection.
Emerging Regulatory Drivers for SBOM and Escrow
SBOM adoption is being driven by regulation across multiple regions. Escrow complements these requirements by addressing continuity risk.
Key frameworks include:
- EU Cyber Resilience Act (CRA): requires SBOMs for products with digital elements
- DORA: requires financial entities to manage ICT third-party risk
- CISA guidance: promotes SBOM use for software supply chain security
These frameworks focus on software bill of materials cyber security and software supply chain transparency. They also reflect a broader shift toward operational resilience.
Organizations are expected to understand their dependencies and maintain control over them.
SBOMs provide visibility into software components and vulnerabilities. Escrow provides the ability to rebuild and operate software if a vendor fails.
Together, SBOM software escrow supports both transparency and continuity. It allows organizations to identify risk and maintain operations under failure conditions.
Turning SBOM Into Real Continuity
SBOMs provide visibility into software components and dependencies. They do not ensure systems can be rebuilt or operated during vendor failure. A verified Software escrow deposit provides that capability.
Together, SBOM software escrow connects transparency with recovery. It allows organizations to identify risk and maintain operations under disruption.
For teams managing critical third-party software, this approach is becoming standard. PRAXIS can help assess which systems require coverage and structure escrow programs with verified, buildable deposits.
Frequently Asked Questions
What is an SBOM and how does it relate to software escrow?
An SBOM is a machine-readable inventory of all software components and dependencies. An SBOM provides visibility into what is in the software, including dependencies and versions. It is widely required under frameworks such as U.S. Executive Order 14028 and supported by Cybersecurity and Infrastructure Security Agency. Software escrow complements this by ensuring the software can be rebuilt and used if the vendor is no longer available.
What should be included in a software escrow deposit alongside an SBOM?
A complete escrow deposit must include all components required to rebuild the software described in the SBOM.
An SBOM alone is not enough. You need everything required to recreate the software. A complete deposit typically includes:
- Full source code (version-controlled)
- Third-party dependencies matching the SBOM
- Build environment (scripts, compilers, containers)
- Technical documentation (architecture, deployment, configuration)
This combination ensures SBOM software continuity, not just visibility. Without these components, the SBOM becomes a reference document, not a recovery solution.
Who should require SBOM escrow in vendor contracts?
Organizations that rely on critical third-party software should require SBOM software escrow in vendor contracts. This is most relevant for regulated industries such as financial services, healthcare, defense, and critical infrastructure. It is also increasingly used by government contractors working under U.S. Executive Order 14028 and organizations aligning with Cybersecurity and Infrastructure Security Agency guidance or zero-trust frameworks. In practice, this appears in procurement and RFP requirements as part of standard vendor risk management.
How do SBOMs and software escrow work together for supply chain resilience?
SBOMs and escrow address different risks in the software supply chain. An SBOM provides software supply chain transparency. It allows organizations to identify dependencies and assess vulnerabilities quickly. Escrow addresses continuity. If a vendor fails or a product is discontinued, escrow provides access to verified source code and build assets so systems can continue to operate. Together, SBOM software escrow connects visibility with recoverability.
Which regulations are driving SBOM and escrow requirements?
Several frameworks are driving SBOM adoption. In the United States, U.S. Executive Order 14028 requires SBOMs for federal software suppliers. This is supported by guidance from Cybersecurity and Infrastructure Security Agency on software supply chain security. In Europe, the EU Cyber Resilience Act requires SBOMs for products with digital elements. The Digital Operational Resilience Act requires financial institutions to manage ICT third-party risk. The direction is consistent. Software supply chain transparency is becoming a baseline requirement. Escrow is increasingly used alongside it to address continuity and operational risk.

Chris Smith Author
Chris Smith is the Founder and CEO of PRAXIS Technology Escrow and a recognized leader in software and SaaS escrow with more than 20 years of industry experience. He pioneered the first automated escrow solution in 2016, transforming how escrow supports Agile development, SaaS platforms, and emerging technologies.

