Introduction
Most enterprises run critical operations on SaaS and cloud platforms they do not control. That dependency becomes a risk when a vendor is acquired, changes its product, raises pricing, or shuts down.
For business-critical systems such as ERP, banking infrastructure, or clinical platforms, downtime is not acceptable. In some cases, it creates regulatory exposure.
A cloud exit strategy defines how an organization maintains operations when a provider is no longer viable. It is a core part of cloud continuity planning, not just migration.
For systems that must continue running, escrow in cloud environments provides the mechanism to rebuild and operate independently. This is where cloud escrow for business becomes part of practical exit planning.
What Is a Cloud Exit Strategy?
A cloud exit strategy is a documented plan for transitioning away from a cloud or SaaS provider without disrupting operations.
It applies in scenarios such as:
- Vendor failure or insolvency
- Commercial disputes
- Acquisition with product discontinuation
- End-of-life announcements
- Strategic decisions to move platforms
A usable strategy includes four core components:
- Data portability, exporting data in a structured and usable format
- Application continuity, maintaining the functionality the platform provided
- Integration preservation, keeping connections to other systems intact
- Transition timeline, defining how long the migration will take
Exit does not always mean switching providers. It can also involve a cloud repatriation strategy, where systems move back to controlled infrastructure.
Most organizations focus on onboarding, not exit. Data export alone is not sufficient. Restoring application functionality can take weeks or months depending on system complexity. This is why SaaS exit planning is often incomplete.
The Cloud Vendor Lock-In Risk
Cloud vendor lock-in occurs when switching providers becomes too costly or complex to execute.
A cloud exit strategy is necessary because, without it, organizations become dependent on systems they cannot easily replace.
Lock-in typically appears in four forms:
- Technical lock-in: proprietary APIs, data formats, or infrastructure that cannot be migrated easily
- Contractual lock-in: long-term agreements or exit penalties that limit flexibility
- Operational lock-in: workflows tightly coupled to vendor-specific systems
- Financial lock-in: sunk costs in integrations, training, and customization
For business-critical applications such as ERP, core banking, clinical systems, and trading platforms, this is not just an inconvenience. It is an operational and regulatory risk.
Replacing or rebuilding these systems can take months. During that time, operations and compliance are exposed.
Without a defined exit path, staying with a vendor becomes a constraint, not a decision.
Where Software Escrow Fits in a Cloud Exit Strategy?
Software escrow fits into a cloud exit strategy by enabling an organization to operate the software independently if the vendor fails or discontinues the service.
It addresses the point where migration is not immediate and continuity must be maintained.
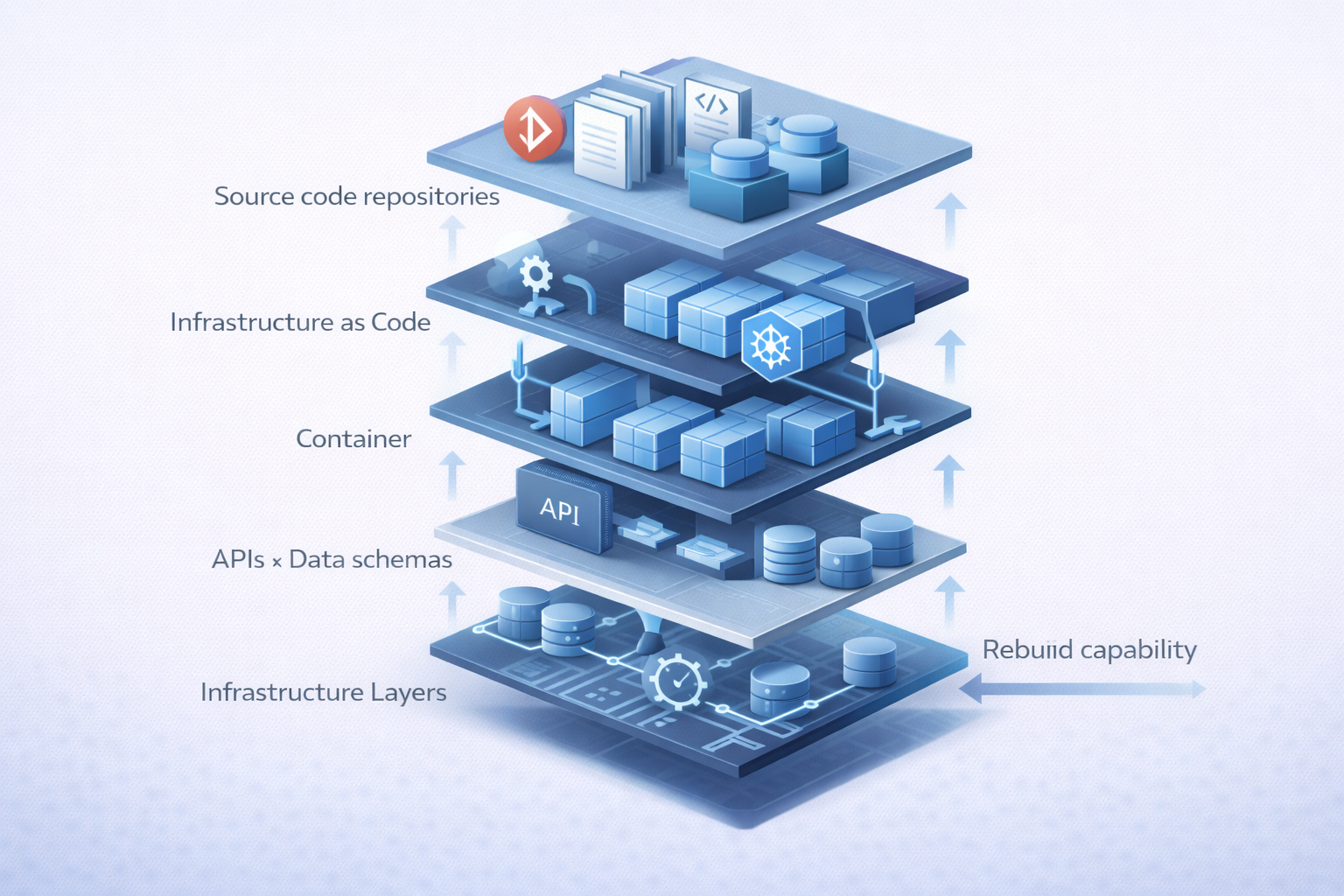
Cloud-based systems require more than source code. A usable escrow deposit must include the full stack needed to rebuild and run the application.
A complete escrow in cloud environments includes:
- Source code and build instructions
- Infrastructure-as-code configurations
- Deployment scripts and environment settings
- Data schemas and export procedures
- API documentation and integration specifications
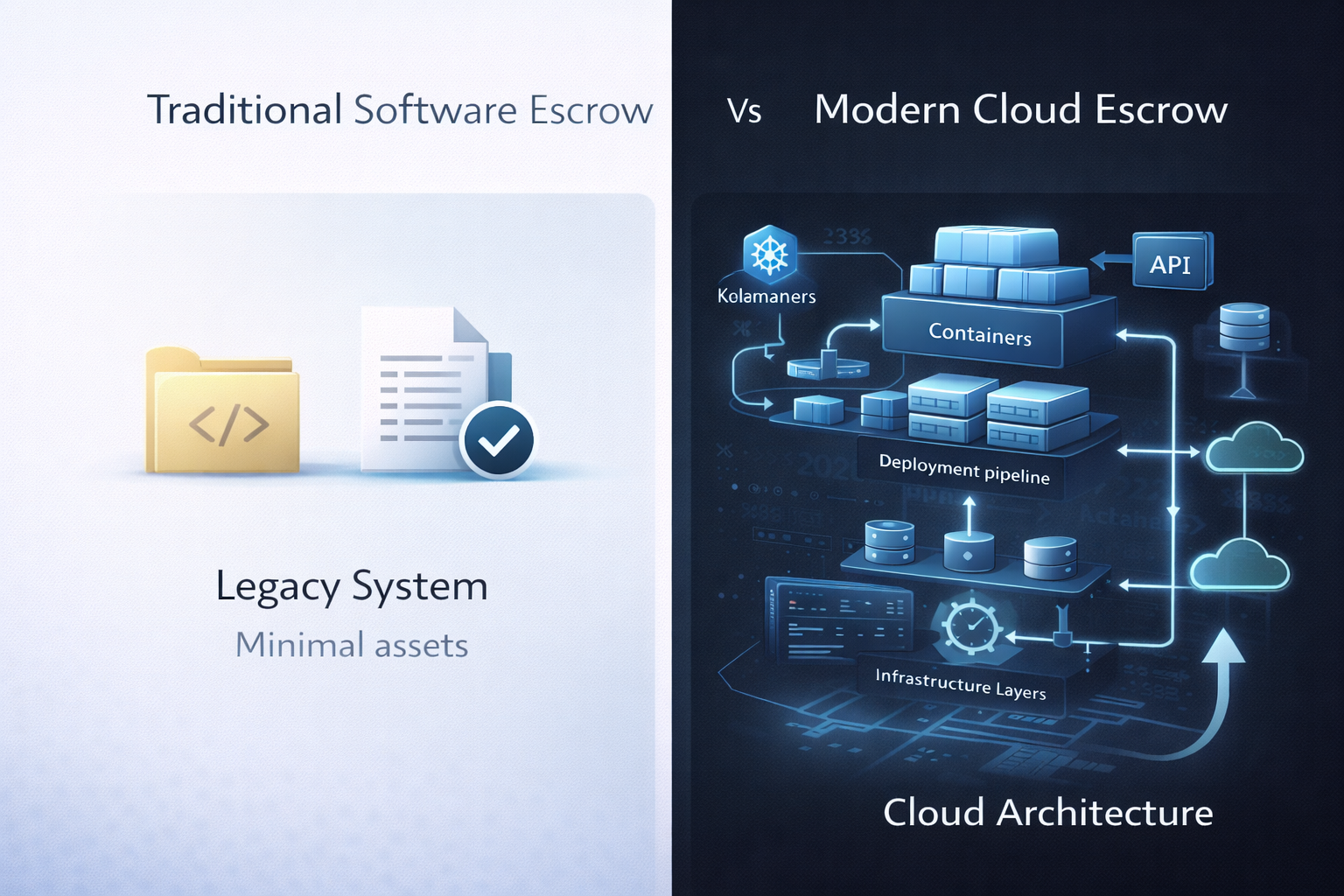
This is the key difference from traditional escrow. Traditional models provide access to code. Cloud escrow provides the ability to rebuild and operate the system.
Escrow activates under defined conditions:
- Vendor insolvency
- Acquisition with product discontinuation
- Material SLA breach
- End-of-life without adequate transition support
Without escrow, the organization remains dependent on the vendor. With it, systems can continue operating during transition.
For business-critical applications, cloud escrow for business is a practical component of cloud continuity planning.
Building a Cloud Exit Strategy That Actually Works
Understanding the risks is one thing. Building a strategy that works under pressure is another.
Here’s a practical framework:
Step 1 — Inventory Critical Cloud Dependencies
Start with visibility.
Identify which systems would cause immediate disruption if unavailable. Prioritize based on operational and regulatory impact.
Ask: What breaks if this system is down for 24 hours?
This is the foundation of effective cloud continuity planning.
Step 2 — Assess Data Portability
Evaluate how easily your data can move.
- Can it be exported in formats like CSV or JSON?
- Are there dependencies on proprietary schemas?
- How long does extraction take?
A cloud exit strategy fails quickly if data can’t be extracted cleanly.
Step 3 — Evaluate Escrow Coverage
Map your critical systems against escrow protection.
- Which vendors already have escrow agreements?
- Which critical platforms have no coverage?
This is where cloud escrow for business becomes a requirement, not a nice-to-have.
Step 4 — Define Activation Scenarios
Your plan needs clear triggers.
Document when you would activate your exit:
- Vendor insolvency
- SLA breaches
- Product discontinuation
- Contract termination events
Clear triggers align legal, technical, and operational teams when decisions need to be made quickly.
Step 5 — Test the Plan
A plan that hasn’t been tested won’t hold up.
Run tabletop exercises:
- Simulate a vendor outage
- Test data extraction
- Validate dependencies and timelines
For example: Can you restore core functionality within 72 hours?
If not, your assumptions need adjusting.
Step 6 — Embed Exit Rights in Contracts
Everything above needs to be enforceable.
Negotiate protections during contract discussions:
- Data portability rights
- Escrow requirements
- Transition support obligations
Adding these after an issue arises is rarely successful.
What to Include in Vendor Contracts for Cloud Exit Protection
Vendor contracts determine whether a cloud exit strategy works in practice. Exit rights must be defined before issues occur, not during a disruption.
Key contract provisions include:
- Data portability clause: Right to export all data at any time and upon termination, in standard machine-readable formats, with no additional fees
- Escrow requirement: Escrow in cloud environments should cover source code, deployment assets, and infrastructure configuration needed to rebuild and operate the system
- Transition assistance: Vendor obligation to provide support during transition, typically 90 to 180 days
- Business continuity provisions: Advance notice of acquisition, product discontinuation, or significant pricing changes
- Audit rights: Ability to verify escrow deposits and test data export procedures through technical validation
These terms ensure that exit planning is enforceable and support effective cloud continuity planning.
Regulatory Drivers for Cloud Exit Planning
Regulators increasingly expect organizations to maintain a documented cloud exit strategy for critical systems. This is now part of standard risk and continuity requirements across sectors.
Key frameworks include:
- DORA (EU financial sector): Requires documented exit strategies for ICT third-party providers as part of operational resilience
- FFIEC (US financial institutions): Expects formal exit planning for critical technology vendors
- HIPAA (healthcare): Implies continuity requirements for systems handling protected health information
- ISO 22301 (business continuity management): Includes exit strategies for critical dependencies within business continuity programs
In practice, exit planning is reviewed during vendor risk assessments and compliance audits.
Organizations are expected to demonstrate how they maintain operations if a provider fails.
Building a cloud exit strategy early is more effective than responding under audit pressure.
Conclusion
A cloud exit strategy only works if it’s defined before something goes wrong, and for critical systems, that preparation is what keeps operations running. Cloud escrow turns continuity from a plan into something you can actually execute, with the assets and verification to back it up.
PRAXIS supports enterprise teams with SOC 2–certified escrow, Automated Escrow workflows, Infinite Retention, and hands-on technical verification. If you’re reviewing key vendors or updating contracts, it’s worth checking where your exit plan holds and where it doesn’t.
If you want a second set of eyes on that, we’re here to help.
Frequently Asked Questions

What is a cloud exit strategy and why does it matter?
A cloud exit strategy is a documented plan for transitioning away from a SaaS or cloud provider without disrupting operations. It matters because replacing a critical system can take 6 to 12 months, and most migrations take weeks to months even under controlled conditions.
How does software escrow fit into a cloud exit strategy?
Software escrow fits into a cloud exit strategy by providing the assets required to operate independently if a vendor fails. It ensures you can rebuild and run the system, not just retrieve your data.
What should be included in cloud software escrow beyond source code?
Cloud escrow should include infrastructure configurations, deployment scripts, data schemas, and integration documentation. Modern setups often rely on Git repositories and container environments like Docker or Kubernetes.
How do you negotiate cloud exit protections in vendor contracts?
You negotiate cloud exit protections by defining data portability, escrow, and transition requirements during contract discussions. This includes data export rights, escrow coverage, transition support for 90 to 180 days, and audit rights to verify deposits and processes.
Which regulations require documented cloud exit strategies?
Several regulatory frameworks require or expect documented cloud exit strategies for critical systems. Examples include DORA, FFIEC guidance, HIPAA, and ISO 22301, which are commonly reviewed during audits and vendor risk assessments.

